Our thoughts on the future of digital innovation and the cloud.

What is Azure Lighthouse?
Azure Lighthouse is the central location for Cloud Service Providers (CSPs) to view and manage Azure resources across all their customers with higher automation, scale, and enhanced governance.
That is right, it means management at scale.
But is it only for Managed Service and Cloud Service Providers like us? No, enterprise IT organizations can also benefit from Azure Lighthouse for managing resources across their multiple tenants.
Basically, it gives you capabilities to manage multiple subscriptions of multiple tenants from one tenant. It improves security and provides more transparency.
This is a new functionality built into Azure.
What is life like without Azure Lighthouse?
Toggling between tenants:
If you are managing multiple tenants and subscriptions for your organization, you are either:
- accessing those subscriptions by assigning a role on the target subscription to your guest account and then switching tenants from your account, or
- creating a user in the client’s tenant, assigning a role to the new user and logging in to their tenant with your new credentials.
Either of these is annoying and time consuming if you have quite few tenants to manage, plus it is not secure.
The other way that you might be accessing those subscriptions is through the Microsoft Partner Center. In that case you are using the “Administrator On Behalf Of” (AOBO) and assigning users to an Admin Agent Role. But do you want to give all users full access to all resources in the target subscriptions? Plus, the Admin Agent role is not tenant or subscription specific; rather, it works across the Partner Center and will apply to all customers. What if one customer does not want you to have that level of access to their subscriptions?
By using Azure Lighthouse, you get cross-tenant management without having to configure users on each subscription one by one. Plus, you can give users different levels of access to the resources.
Messy permissions
When we assign a role to each user to access a resource, we are usually not thinking that in future there may be more users with the same level of access to the same resource. At some point, we realize there are a lot of individual users accessing the same resource, and that it is hard to manage them.
By using Azure Lighthouse, you automatically lean toward creating groups for users who need different level of access.
Repeated Tasks
I am quite sure that most of you would like to monitor resource state, service health, and compliance over multiple environments and automate actions based on findings for all resources without need of per-subscription or per-tenant configuration.
This is now achievable by deploying Azure Lighthouse Azure delegated resource management.
What is Azure delegated resource management?
This is exactly what you need to implement in order to perform management operations across different Azure AD tenants.
How does it work?
Take some time to specify which groups, service principals, and users can manage customers’ Azure resources. You can specify separate groups by customer or role, and then make your users part of the groups.
Then use Azure sample ARM templates in JSON format, edit the parameters and user PowerShell or CLI commands to deploy the template in customer’s tenant.
Alternatively, you can publish an Azure Marketplace managed offer.
How do you access customers’ subscriptions after deploying Azure delegated resource management?
There are two ways:
- From your CSP tenant, go to the “My Customers” page to see all the customers subscriptions that you have access to. Customers similarly can go to the “My Providers” page to see their CSP providers and their accesses.
- From you CSP tenant, go to Directory + subscription from the top menu bar and select the directories and subscriptions that you want to see in your tenant directly. After that you can have more options at resource levels to filter out the subscriptions that you want to see.
How does it look when you have Azure Lighthouse?
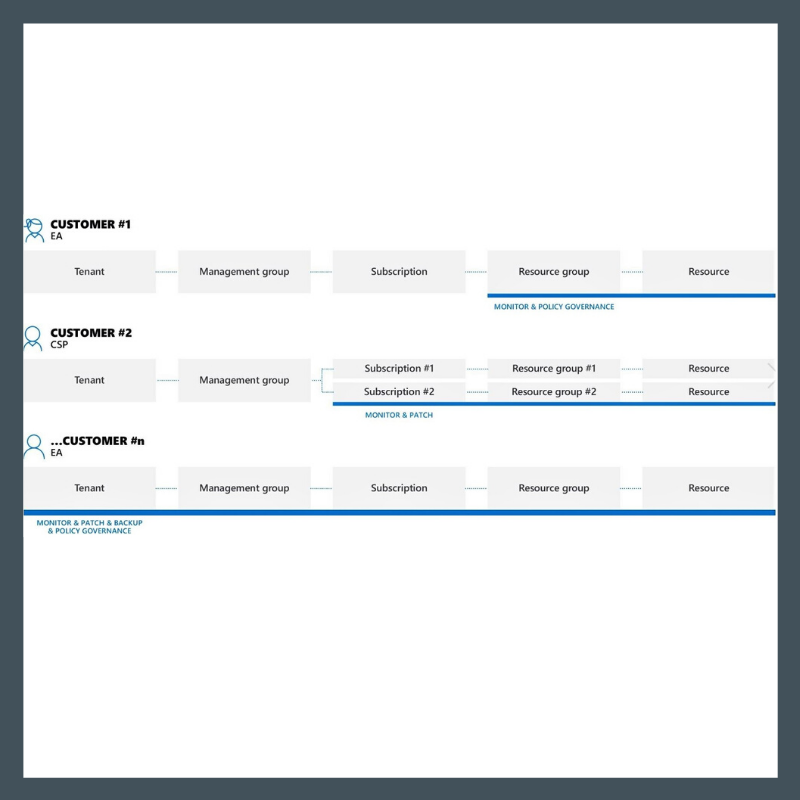
Tenant management without Azure Lighthouse:
Tenant management with Azure Lighthouse:
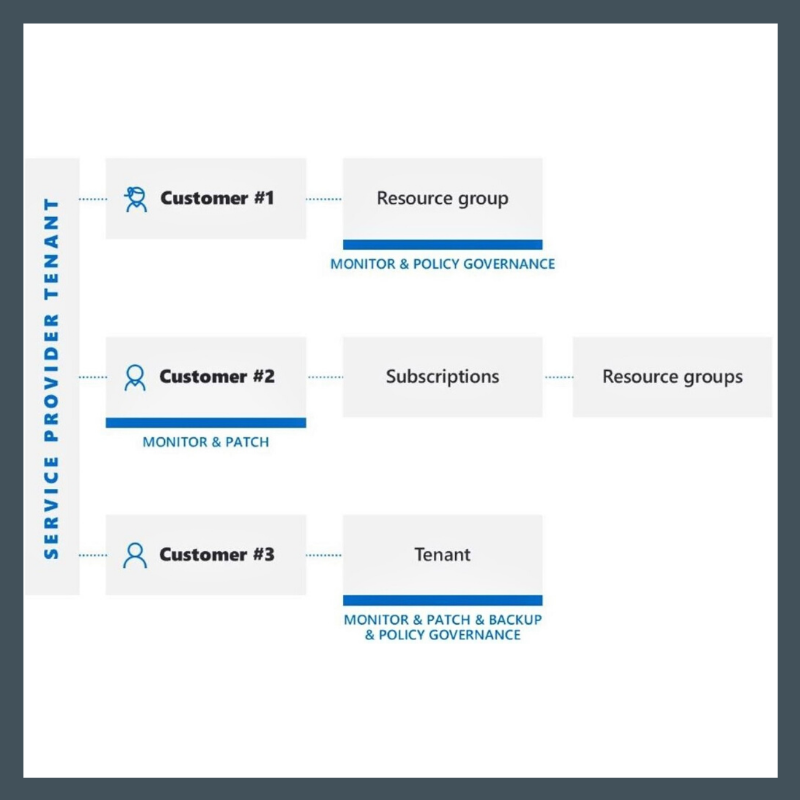
You have probably heard this referred to as a cross-tenant management experience.
Security Considerations
Now that you are accessing all customers’ tenants and resources from your tenant, you are responsible for keeping your security principals even more secure because if it gets compromised, a hacker can access not only your resources but all those customers within that same location.
How do you keep your tenant secure? Here are three practices that help:
- Apply Multi Factor Authentication (MFA) to all your security principals who have access to customers’ tenants.
- Remember the principle of least privilege. Assign the permissions that are necessary for managing customers’ resources, and no more than that. Just to mention that Azure PIM is working here as well; you can limit access to a specific time, and manage using approval processes.
- Always use Group Assignment instead of individual access to customers’ subscriptions.
Give Azure Lighthouse a try…. It is a good experience when you can see and edit Azure Alerts, Backups, Polices, and run queries against all customers’ subscriptions from one location.

